Company Profile
▼Legal Name
Meridian Precision Defense Systems, Inc. (MPDS)
CAGE Code
7RK42
UEI Number
MPDS2024UEI881
Year Founded
1998
Ownership
Privately held — ESOP (~72% employee-owned, 28% founding family)
Primary NAICS
332995 — Other Ordnance and Accessories Manufacturing
Secondary NAICS
541330 — Engineering Services
Revenue Range
$28M–$34M annually (FY2024 estimate)
Employees
147 total — 112 Dayton OH · 35 Huntsville AL
FOCI Status
No known foreign ownership, control, or influence. Annual review completed March 2025.
Locations
▼Headquarters — Primary Site
1440 Industrial Parkway
Dayton, OH 45401
112 employees · All servers on-prem here · Primary CUI processing
Secondary Site
820 Technology Drive
Huntsville, AL 35806
35 employees · Systems Integration Team · Connected via IPsec VPN to Dayton
Core Competencies
▼- Precision machining and fabrication of guidance system housings and actuator assemblies
- Systems integration support for unmanned aerial vehicle (UAV) subsystems
- Technical data package (TDP) development and configuration documentation
- Defense acquisition lifecycle support — engineering change proposals, failure analysis
Contract 1 — Army Prime Contract (W58RGZ-23-C-0174)
▼| Contract Number | W58RGZ-23-C-0174 |
| Agency | U.S. Army Aviation and Missile Command (AMCOM), Redstone Arsenal, AL |
| Type | Firm Fixed Price (FFP) |
| Value | $11.4M |
| Period of Performance | 01 Oct 2023 – 30 Sep 2026 |
| Deliverables | Actuator housing assemblies (NSN 1270-01-594-3311); associated TDPs; qualification test reports |
| CUI Categories | CUI//CTI EAR99 Baseline ITAR-Controlled Drawings |
| DFARS Clauses | 252.204-7012 252.204-7019 252.204-7020 252.204-7021 |
| Classified? | No — all CUI, no classified information |
Contract 2 — Raytheon Subcontract (RTX-SUB-2024-4489)
▼| Subcontract Number | RTX-SUB-2024-4489 / Prime: FA8650-24-C-0033 |
| Agency (via Prime) | AFLCMC, Wright-Patterson AFB, OH (Raytheon Technologies prime) |
| Type | Cost Plus Fixed Fee (CPFF) subcontract |
| Value | $4.7M |
| Period of Performance | 15 Mar 2024 – 14 Mar 2027 |
| Deliverables | UAV airframe bracket design support; FEA reports; engineering drawings per MIL-DTL-31000C |
| CUI Categories | CUI//CTI CUI//PRVCY (limited) ITAR — 22 CFR Part 121 |
| DFARS Clauses | 252.204-7012 252.225-7048 Flow-down from Raytheon prime |
Contract 3 — NAVAIR SBIR Phase II (N68335-22-C-0552)
▼| Contract Number | N68335-22-C-0552 |
| Agency | Naval Air Systems Command (NAVAIR), Patuxent River, MD |
| Value | $1.85M |
| Period of Performance | 01 Jun 2022 – 31 May 2025 (final reports phase) |
| Deliverables | R&D prototype — lightweight composite actuator; final technical report |
| CUI Categories | CUI//CTI CUI//SP-EXPT |
| DFARS Clauses | 252.204-7012 |
Key Personnel — Cybersecurity Responsibilities
▼| Name | Title | Cybersecurity Role |
|---|---|---|
| Marcus T. Ellison | President / CEO | Authorizing Official (AO) — signs risk acceptance; CMMC compliance sponsor |
| Diana L. Kowalczyk | CISO / IT Security Manager | SSP owner; policy oversight; IR coordination; CMMC assessment lead; POA&M management |
| Trevor J. Nakamura | IT Administrator / Sys Admin | Day-to-day sysadmin; patch mgmt; account provisioning; backup mgmt; log collection |
| Priya S. Mehta | Contract Manager | DFARS clause tracking; CUI flow-down requirements; supplier agreements |
| Renata M. Bauer | HR Director | Personnel security; background checks; onboarding/offboarding; SAT enrollment |
| Gregory A. Farris | FSO / Physical Security Mgr | Physical access control; visitor management; media destruction; DISS records |
Third-Party Relationships
▼| Party | Role | CUI Access? | Notes / Gaps |
|---|---|---|---|
| ClearPath IT Solutions | Managed Service Provider (MSP) | YES | Remote admin via VPN · Month-to-month · No DFARS flow-down · No CMMC requirement in contract |
| Microsoft (M365 GCC High) | Cloud productivity suite | YES | FedRAMP High authorized · Meets ITAR/CUI for GCC High · Partially configured (see §IT) |
| AWS GovCloud (US-West) | Cloud compute — SBIR analysis | YES | FedRAMP High authorized · MPDS manages IAM directly · Root account MFA enabled |
| Whitmore & Associates LLC | External accounting (CPA) | NO | Read-only QuickBooks; not in SSP scope |
In-Scope Systems
▼| System ID | Name | Type | Platform | Location | CUI? |
|---|---|---|---|---|---|
| SYS-001 | MPDS-CORP-DC01 | AD Domain Controller | Windows Server 2019 | Dayton | Yes |
| SYS-002 | MPDS-CORP-DC02 | AD Secondary DC / DNS | Windows Server 2019 | Dayton | Yes |
| SYS-003 | MPDS-FILE-SRV01 | Windows File Server | Windows Server 2022 | Dayton | PRIMARY |
| SYS-004 | MPDS-APP-LNX01 | Linux App Server — PLM | Ubuntu 22.04 LTS | Dayton | Yes |
| SYS-005 | MPDS-ENG-WS (×14) | Engineering Workstations CAD/CAM | Windows 10 Enterprise 22H2 | Dayton | Yes |
| SYS-006 | MPDS-HVL-WS (×6) | Engineering Workstations | Windows 11 Enterprise | Huntsville | Yes |
| SYS-007 | M365-GCC-HIGH | M365 GCC High Tenant | Cloud — Microsoft | Cloud | Yes |
| SYS-008 | AWS-GOVCLOUD-ENV | AWS GovCloud Compute/S3 | Cloud — AWS | Cloud | Yes |
| SYS-009 | MPDS-FW-01 | Perimeter Firewall | Fortinet FortiGate 200F | Dayton | No |
| SYS-010 | MPDS-VPN-GW | VPN Gateway | FortiGate 200F (module) | Dayton | No |
| SYS-011 | MPDS-IDS-01 | IDS/IPS Sensor | Snort 3.x on Ubuntu 20.04 | Dayton | No |
| SYS-012 | MPDS-PRNT-01 | MFP Printer/Scanner | Xerox AltaLink C8045 | Dayton | Yes |
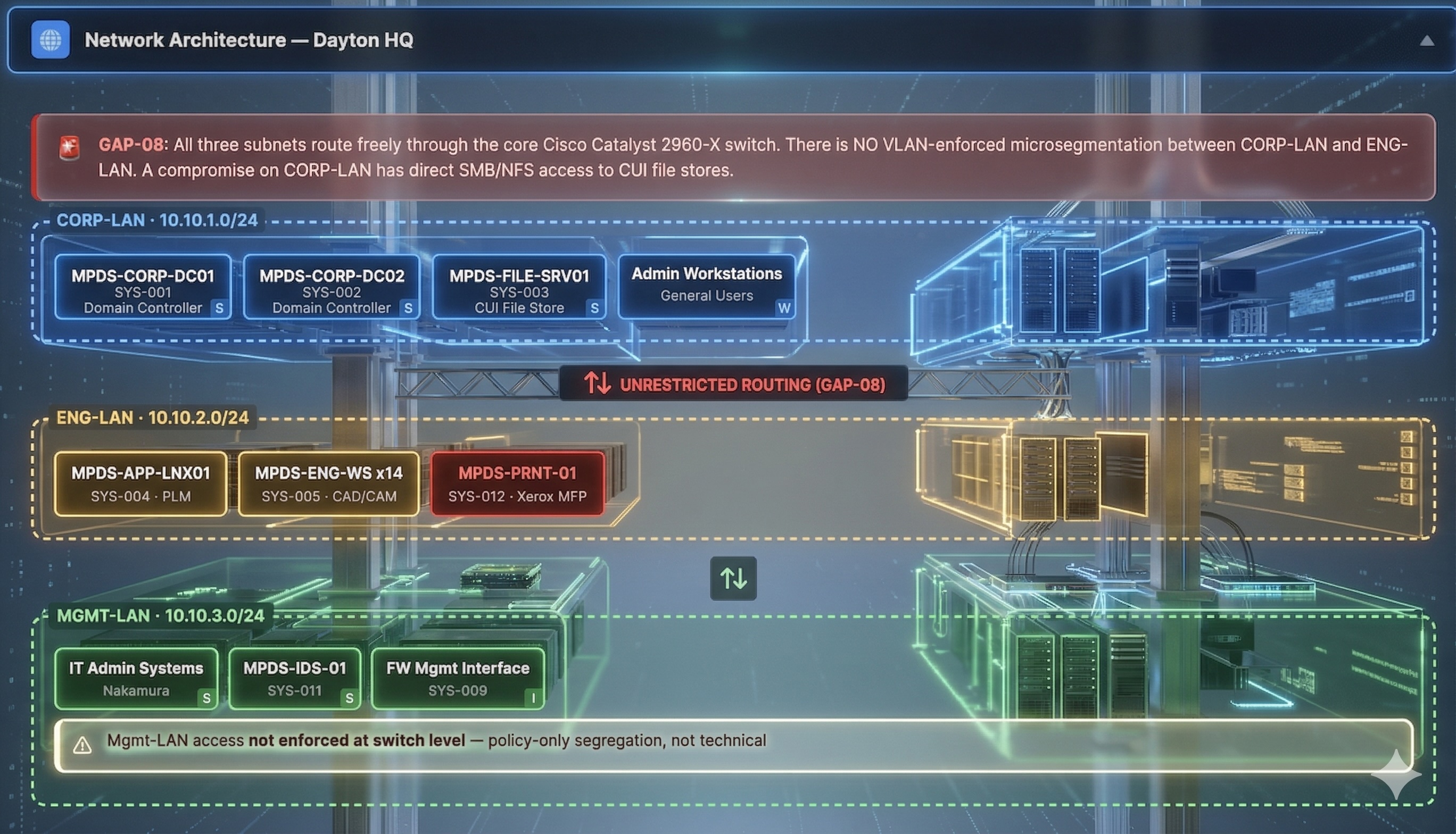
Network Architecture — Dayton HQ
▼Single ISP · 1Gbps · No DMZ · IPsec VPN on SYS-010
CUI Data Flow
▼SFTP / Encrypted Email
SYS-007 · Email receipt
SYS-003 · Primary CUI store
SYS-004 · Drawings, BOMs
SYS-005/006 · CAD/CAM
Hard-copy CUI output
⚠ No automated control
SYS-008 · FEA data
Existing Policies & Documents
▼| ID | Document Title | Version | Last Reviewed | Status |
|---|---|---|---|---|
| POL-001 | Access Control Policy | 1.2 | Jan 2024 | Current |
| POL-002 | Incident Response Plan | 1.0 | Mar 2022 | Stale — 3+ yrs |
| POL-003 | Configuration Management Plan | 1.1 | Sep 2023 | Aging |
| POL-004 | Media Protection Policy | 1.0 | Nov 2021 | Stale — 4+ yrs |
| POL-005 | Security Awareness Training Program | 2.0 | Feb 2024 | Current |
| POL-006 | Risk Assessment Report | — | Jun 2023 (19+ mo ago) | Overdue |
| POL-007 | System & Communications Protection Policy | 1.0 | Aug 2022 | Stale — 3+ yrs |
| POL-008 | System Security Plan (SSP) | 2.1 | Oct 2023 | Needs update |
| POL-009 | Physical Security Plan | 1.3 | Jan 2024 | Current |
| POL-010 | Contingency / Business Continuity Plan | 0.9 DRAFT | Never finalized | Draft — not approved |
Identified Security Gaps (8 Seeded Findings)
▼GAP-01 — MFA Not Enforced on SSL VPN
IA- Domain
- IA — Identification & Authentication
- Practice
- 3.5.3 — Use multifactor authentication for local and network access
- Finding
- Remote access to all in-scope systems is accessible with username/password only. MFA is enforced only at the M365 layer, not at the network access (VPN) layer.
- Evidence Needed
- VPN configuration screenshots; authentication logs; MFA policy documentation
GAP-02 — Six Stale VPN Accounts for Separated Employees
AC- Domain
- AC — Access Control
- Practices
- 3.1.1 — Limit system access to authorized users; 3.1.2 — Limit system access to transactions and functions users are authorized to execute
- Finding
- Six VPN accounts for separated employees remain active. No automated deprovisioning tie-in between Convergent HR and AD/VPN gateway.
- Root Cause
- Offboarding email notification process — VPN deprovisioning not included in offboarding checklist
GAP-03 — Audit Logs Not Regularly Reviewed; 30-Day Retention
AU- Domain
- AU — Audit & Accountability
- Practices
- 3.3.1 — Create and retain system audit logs; 3.3.2 — Ensure actions of individual users can be traced
- Finding
- SYS-003 and SYS-004 generate logs but no formal review process exists. Retention is 30 days (below 90-day minimum). No SIEM deployed.
- Evidence Needed
- Log retention configuration; review schedule / ticketing records; SIEM or equivalent documentation
GAP-04 — No Asset Inventory; Unpatched Engineering Workstations
CM- Domain
- CM — Configuration Management
- Practices
- 3.4.1 — Establish and maintain baseline configurations; 3.4.2 — Establish and maintain a component inventory
- Finding
- Engineering workstations (SYS-005 ×14) not enrolled in any configuration management tool. ~4 workstations are 90+ days behind on critical Windows Updates. No formal asset inventory exists.
- Evidence Needed
- Patch management reports; WSUS/SCCM enrollment; configuration baseline documentation
GAP-05 — No Formal POA&M; Informal Spreadsheet Not AO-Approved
CA- Domain
- CA — Security Assessment
- Practice
- 3.12.4 — Develop, document, and periodically update system security plans
- Finding
- Kowalczyk maintains an informal spreadsheet (stored in personal OneDrive — NOT GCC High). It has no version control, no remediation owners, no target dates, no resource estimates, and has not been reviewed by the AO in 18+ months.
- Additional Gap
- POA&M stored outside the authorized CUI boundary (personal OneDrive vs. GCC High tenant)
GAP-06 — No Supply Chain Risk Management Program
SR- Domain
- SR — Supply Chain Risk Management
- Practices
- 3.17.1 — Assess cybersecurity risks associated with suppliers; 3.17.2 — Use SCRM plans to reduce risk
- Finding
- MPDS has not assessed the cybersecurity posture of ClearPath MSP or any hardware/material suppliers. MSP contract contains no DFARS flow-down, no right-to-audit, and no cybersecurity requirements.
- Scope
- Affects ClearPath MSP, Acuitas Machining (receives CUI drawings), Secure Shred AL (handles CUI paper, no NDA)
GAP-07 — IRP Not Tested Since 2022; Missing DIBCAC Reporting Language
IR- Domain
- IR — Incident Response
- Practices
- 3.6.1 — Establish an IR capability; 3.6.2 — Track, document, and report incidents; 3.6.3 — Test the IR capability
- Finding
- No tabletop exercise since IRP creation (2022). IRP lacks DFARS 72-hour reporting requirement language. Contact list includes former employee (Chen, PM — departed early 2024).
GAP-08 — No Network Segmentation Between CORP-LAN and ENG-LAN
SC- Domain
- SC — System & Communications Protection
- Practice
- 3.13.3 — Separate user functionality from system management functionality
- Finding
- CUI on ENG-LAN (SYS-003, SYS-004, SYS-005) is reachable from CORP-LAN without restriction. A workstation compromise on CORP-LAN provides direct SMB/NFS access to all CUI file stores.
Onboarding & Offboarding
▼Onboarding
- Background check via HireRight prior to Day 1 (criminal, employment, education)
- CUI Handling Agreement (Form HR-07) signed before AD account provisioned
- IT provisioning via manual ticket from HR — avg. lag 1–2 business days
Offboarding — GAPS
- HR notifies IT via email only — no formal workflow or checklist
- Average AD account disable lag: 3–7 business days after separation
- VPN deprovisioning NOT part of standard offboarding (source of GAP-02)
- Physical badge deactivation done by FSO Farris — generally same day
Security Awareness Training
▼Platform
KnowBe4 (annual subscription)
Frequency
Annual required training; quarterly phishing simulations
Records Storage
KnowBe4 platform; exported quarterly to M365 GCC High SharePoint
FY2024 Completion Rates
Dayton HQ — Physical Controls
▼| Area | Access Control | Notes |
|---|---|---|
| Main Entrance | HID card reader | Visitor check-in — paper log + photo ID |
| Rear Manufacturing Entrance | HID card reader | Manufacturing staff badge zone |
| Server Room (Room 104) | HID card + PIN keypad | Accessible to Nakamura, Kowalczyk, Ellison. MSP escorted — escort policy informal (not documented) |
| Engineering Area | Corporate badge only | No separate access control — all CORP badge holders can reach ENG workstations |
| Manufacturing Floor | Separate badge zone | Required for floor personnel and visitors |
Huntsville — Physical Security Gaps
▼Media Handling & Destruction
▼| Media Type | Location | Method | Status |
|---|---|---|---|
| Hard-copy CUI | Dayton | Cross-cut shredder (DIN 66399 P-4) | Compliant |
| Hard-copy CUI | Huntsville | Secure Shred AL (offsite vendor) | NO NDA — No CUI handling agreement |
| Digital media (HDD/USB) | Dayton | Degauss + physical destruction, Assured Destruction Services — certs retained | Compliant |
| Decommissioned HDDs ×3 (2022) | Dayton server room | Awaiting disposal in cardboard box | Untracked — No timeline |
Incident History
▼PM Kowalski received a spearphishing email impersonating the Army contracting officer. Kowalski clicked the link; CrowdStrike Falcon (Dayton only) blocked the payload. Informally reported to Nakamura via chat. No formal IR report filed. Kowalczyk learned of it two weeks later in casual conversation. No DIBCAC notification made.
Engineering technician reported losing a USB drive that "may have had some drawing files on it." Drive was unencrypted. No formal investigation. No determination made of whether CUI was on the drive. No DoD notification made. Media Protection Policy prohibits unencrypted removable media — enforcement is policy-only, no technical control.
Open Risk Register
▼| Risk ID | Description | Likelihood | Impact | Level | Remediation | Owner |
|---|---|---|---|---|---|---|
| RISK-01 | Unpatched ENG workstations exploited via network | High | High | Critical | Planned — no target date | Nakamura |
| RISK-02 | MSP privileged access abused or compromised (no MFA, no SCRM) | Medium | High | High | No remediation initiated | Kowalczyk |
| RISK-03 | Stale VPN accounts used by former employee or attacker | Medium | High | High | Partial — HR notified; IT review pending | Nakamura |
| RISK-04 | CUI exfiltrated via unencrypted removable media | Medium | Medium | Medium | Policy exists; no technical enforcement | Kowalczyk / Nakamura |
| RISK-05 | Fire/flood in Dayton server room — no offsite backup for SYS-003 | Low | High | Medium | Backups to local NAS only — no offsite | Nakamura |
| RISK-06 | Huntsville utility closet equipment physically accessed/tampered | Low | Medium | Low-Med | Not addressed | Farris |
Critical Suppliers
▼| Supplier | Role | CUI Access? | DFARS Flow-Down? | Assessment? |
|---|---|---|---|---|
| ClearPath IT Solutions | MSP — remote admin, helpdesk | YES — domain admin | NO | NO |
| FastenerTech Supply | Precision hardware components | No | N/A | N/A |
| AeroComp Composites LLC | Composite structural parts for UAV brackets | 2D drawings via encrypted email | Partial — ref. in PO, not verified | NO |
| Acuitas Machining Inc. | Sub-tier machining overflow | YES — SharePoint link (GCC High) | NO formal agreement | NO |
| Secure Shred AL | Offsite paper shredding (Huntsville) | Physical CUI paper | NO NDA — no CUI handling agreement | NO |
Cloud Service Providers
▼| Provider | Service | FedRAMP | CUI Compliant? | IAM Owner |
|---|---|---|---|---|
| Microsoft M365 GCC High | Email, Teams, SharePoint, OneDrive | High — Authorized | Platform: Yes; Config: Partial | Nakamura (Global Admin) |
| AWS GovCloud (US-West) | Compute, S3 — SBIR analysis | High — Authorized | Yes | Nakamura (root acct, MFA enabled) |
mpds-admin@meridianpds.onmicrosoft.com holds Global Admin rights with no individual owner assigned.Logistics & Delivery Options
▼Group Size
3–5 students per document group (9 groups total; 27–45 students)
Distribution
Full case study to all groups — real auditors review full organizational context
Duration
Recommended 2–3 hours in-class plus 30–60 min prep reading
Deliverable Options
Written findings memo (1–2 pp): list findings, cite NIST 800-171 practice IDs, assign severity, recommend remediation.
Formal audit workpaper in C3PAO style — finding narrative, evidence required, practice met/not met determination.
Mock debrief oral presentation (10 min) to "MPDS executive team" — deliver findings and respond to pushback.